Blog
June 5, 2024
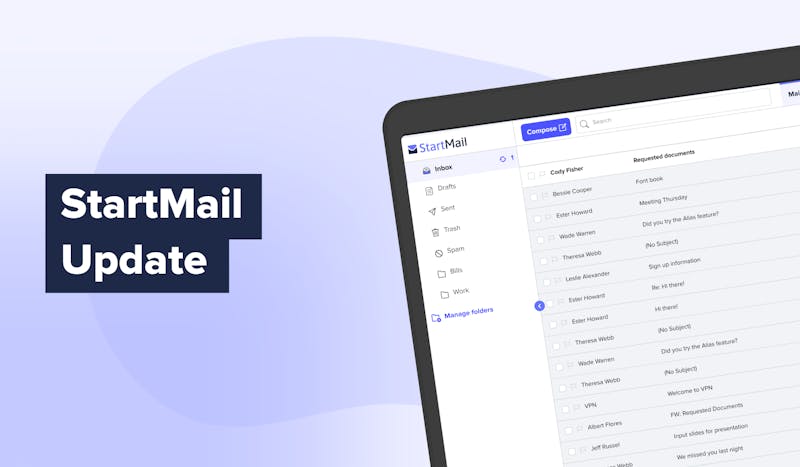
Business Email for Teams – Secure & Private | Work Safely
Discover StartMail’s secure business email for teams – Private, encrypted communication with no tracking. Protect your company’s inbox.
April 9, 2024
Secure Account Recovery & Email Authentication | Article
Learn how StartMail enhances security with account recovery and email authentication – Protect your account and stay in control of your inbox.
April 4, 2024
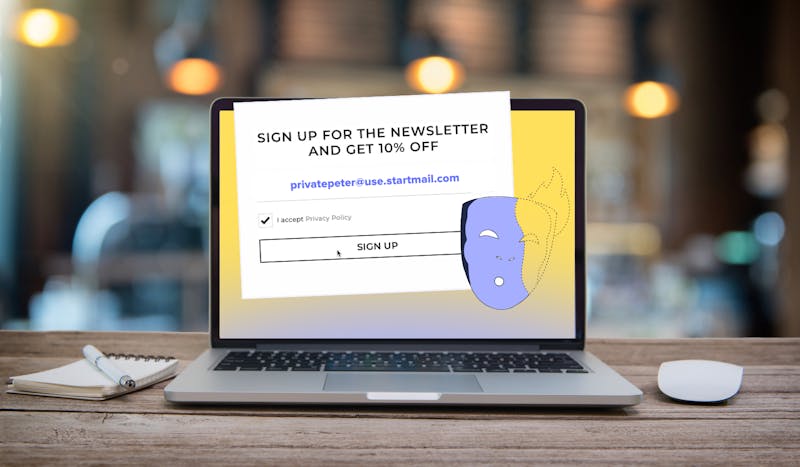
10 Smart Ways to Use a Burner Email – Protect Your Privacy
Discover 10 situations where a burner email keeps you safe – Avoid spam, protect your identity, and stay private online.
March 22, 2024
The Cost of Phishing Scams – Protect Your Data
Explore the impact of phishing scams. Learn real-life examples and strategies to protect yourself and your business from these costly attacks.

February 27, 2024
StartMail’s Long-Term Mission – Committed to Your Privacy
Discover how StartMail has spent over a decade empowering users with secure email services, ensuring control over data without third-party interference.

February 13, 2024
Switch from Skiff to StartMail – Secure Your Email Today
With Skiff shutting down, transition to StartMail for reliable, private email services. Enjoy features like unlimited aliases, encryption, and no ads.

January 24, 2024
World Privacy Day Article – Key Tips to Protect Your Data
Celebrate World Privacy Day by learning how to protect your personal data – Take control of your privacy and stay secure online.

December 15, 2023
US Concerns About Email Security & AI – Survey Results
Explore survey results revealing that 66% of Americans fear email hacks, 62% worry about phishing scams, and 95% are concerned about AI and privacy.

November 17, 2023
Interview with Volla Phone – Founder Dr. Jörg Wurzer
Interview with Volla Phone founder Dr. Jörg Wurzer – A look into Volla's success story, their commitment to privacy, and the future of mobile innovation.

November 14, 2023
Microsoft Outlook Update Raises Privacy Concerns | Blog Article
Learn about the recent Microsoft Outlook update that may compromise your email privacy by transferring messages and credentials to Microsoft's servers, even for non-Microsoft email accounts.