
A Brief History of Data Breaches
A data breach is any incident where confidential or sensitive information has been accessed without permission. Think ransomware, malware, phishing attacks, or system hacks.
They can severely impact businesses and individuals alike. The stolen data may involve your credit card numbers, phone numbers or login details like user names and passwords etc. The financial costs or damage to your reputation and impact on your private life can be huge. Over the last decade, revelation after revelation showed how much our online privacy has come under attack and is eventually exposed.
It’s StartMail‘s mission to help build a safer internet. That’s why we decided early on to build a secure and private platform to help you protect your email data from prying eyes.
To become more aware of the scale and frequency of major data breaches, we have composed a list with the most shocking ones.
The 15 biggest data breaches in history
Adobe
- Date: October 2013
- Impact: 153 million user records
- Monetary value: $1.2 million
- What data was stolen: Usernames, credit card records, and encrypted passwords.
- How did it happen: Hackers’ attack – a portion of Photoshop source code was accessed by the attackers as part of the incident.
Adult Friend Finder
- Date: October 2016
- Impact: 412.2 million accounts
- Monetary value: Unknown
- What data was stolen: 20 years of data including information such as usernames, emails, join dates, and dates of a user’s last visit – the cache may also include 15 million email addresses connected to deleted accounts.
- How did it happen: Potential security vulnerabilities from a variety of sources.
Canva
- Date: May 2019
- Impact: 137 million user accounts
- Monetary value: Unknown
- What data was stolen: Pilfered personal information including real names, usernames, email addresses and city and country information.
- How did it happen: Hackers’ attack.
Dubsmash
- Date: December 2018
- Impact: 162 million user accounts
- Monetary value: $115 million
- What data was stolen: Primarily account holder names, email addresses, and passwords.
- How did it happen: Hacker’s attack.
eBay
- Date: May 2014
- Impact: 145 million users
- Monetary value: $200 million
- What data was stolen: Encrypted passwords, customer names, e-mail addresses, mailing addresses, phone numbers and dates of birth (as reported by eBay).
- How did it happen: Cyber-attack.
Equifax
- Date: July 2017
- Impact: 145 million U.S. consumers
- Monetary value: $1.14 billion
- What data was stolen: Names, addresses, dates of birth, Social Security numbers, and drivers’ licenses numbers, also credit card information.
- How did it happen: The attackers pulled data out of the network in encrypted form undetected for months because Equifax had crucially failed to renew an encryption certificate on one of their internal security tools.
- Date: March and September 2019
- Impact: 540 million and 419 million Facebook users
- Monetary value: Unknown
- What data was exposed: Account names, phone numbers and unique user IDs.
- How did it happen: Exposed Amazon servers.
First American Corporation
- Date: May 2019
- Impact: 885 million records
- Monetary value: Unknown
- What data was exposed: Bank account details, social security digits, wire transactions, mortgages etc.
- How did it happen: Design defects in production applications.
- Date: 2016
- Impact: 117 million user accounts
- Monetary value: $1.25 million
- What data was stolen: Every LinkedIn username and hashed password.
- How did it happen: Cyber-attack.
Marriott International
- Date: April 2014
- Impact: 500 million customers
- Monetary value: $350 million
- What data was stolen: Customer records, including credit card and passport numbers.
- How did it happen: Remote Access Trojan (RAT) along with MimiKatz, a tool for sniffing out username/password combos in system memory.
My Fitness Pal
- Date: February 2018
- Impact: 150 million user accounts
- Monetary value: Unknown
- What data was stolen: Usernames, email addresses, and hashed passwords were all compromised.
- How did it happen: Cyber-attack.
Oxydata
- Date: November 2019
- Impact: reaching more than 1.2 billion people
- Monetary value: Unknown
- What data was stolen: Names, email addresses, phone numbers, LinkedIn and Facebook profile information.
- How did it happen: Unencrypted storage.
- Date: May 2018
- Impact: 330 million users
- Monetary value: Unknown
- What data was exposed: Twitter usernames and passwords.
- How did it happen: Unsecured server.
Yahoo
- Date: 2013-14
- Impact: 3 billion user accounts (record holders.. )
- Monetary value: $117.5 million
- What data was stolen: Names, email addresses, telephone numbers, dates of birth and encrypted passwords.
- How did it happen: Hacked by a state-sponsored actor.
Zynga
- Date: September 2019
- Impact: 218 million user accounts
- Monetary value: Unknown
- What data was stolen: Email addresses, usernames, Login IDs, Facebook IDs, phone numbers, hashed and salted passwords.
- How did it happen: The data breach appears to exclusively affect mobile players who installed the Android or iOS version. The passwords were secured with SHA-1 cryptography, which has been considered outdated and insecure even prior to Zynga’s inception.
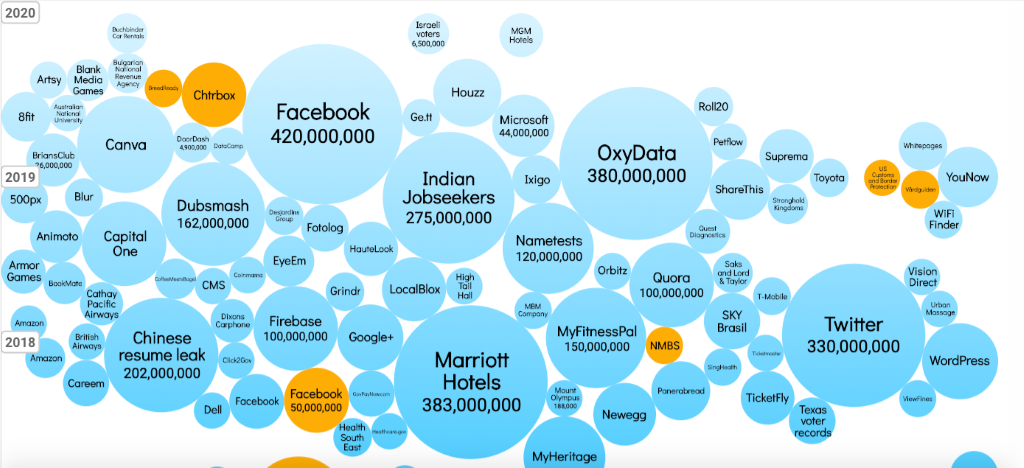
This graph shows the biggest data breaches in terms of users impacted per year. For more data per year, see a full visualisation here. (Source: informationisbeautifull.net) You can clearly see the frequency and extension of the hacks increase quite dramatically over the years….
The Impact of data breaches
For businesses, data breaches can lead to disastrous financial losses impacting their brand and reputation for many years. Between losing customers and therefore revenue, to incurring fines, mediation costs and lawsuits costs, it may be deadly for both small and big businesses. Check out the high average costs for businesses of data breaches below:
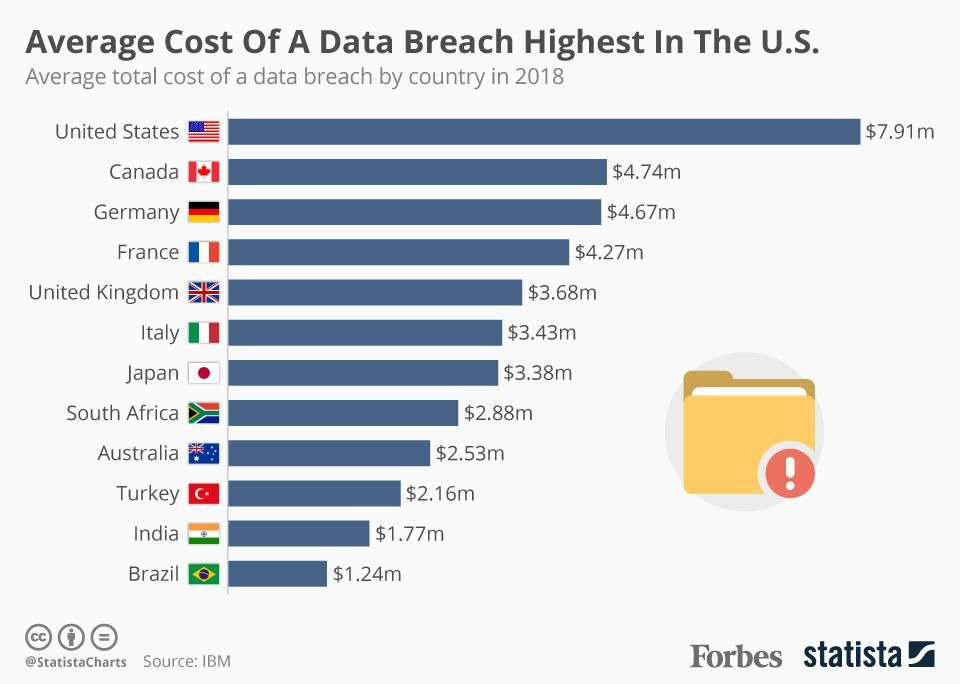
The United States leads with an average cost of $7.91 millions for a data breach, closely followed by Canada and Germany, with a little more than $4.5 million each.
For consumers, the consequences of cybercriminals exploiting their personal data can take a major toll on their personal lives. Here are some examples.
Depending on the information they have, a cyberthief may be able to:
- Impersonate identities through username passwords theft or email hacking
- Open and use new credit cards under the consumer name
- Withdraw money from banking or investment accounts
- File a tax return and take the tax refund
- Get medical treatment using stolen health insurance IDs
- Apply for government benefits
- Open utility or telecom accounts
- Steal and use credit card rewards, such as airline miles
- Sell the consumer identity on the dark web
- Expose email communication
Trends
The trend in number and severity of data breaches has clearly increased
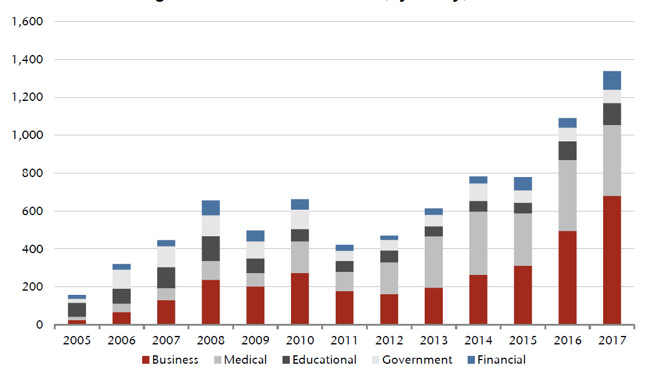
The graph depicts the evolution of data breaches per industry since 2005. The numbers show how quickly the amount of security breaches increased and that this phenomenon isn’t slowing down anytime soon.
The 3 most common causes of data breaches
-
Weak and Stolen Credentials (a.k.a. passwords)
Two-thirds of investigated breaches involved weak, stolen or default passwords. - Ransomware and Malware
Malware is malicious software hackers use to steal information. Trojans, spyware and worms all are forms of malware (also called viruses) that users often install accidentally by clicking on a link (on a site or in an email) or authorizing a download that seems legitimate. - Human error
Unfortunately, mistakes happen and errors are made. Users send sensitive information to the wrong recipients and fall for phishing scams, social engineering etc.
Why do hackers try to get your data?
Cybercrime is a profitable business. Hackers like to steal your personal data because it is worth money. They look for your personally identifiable information to compromise and abuse it or sell it on the Dark Web.
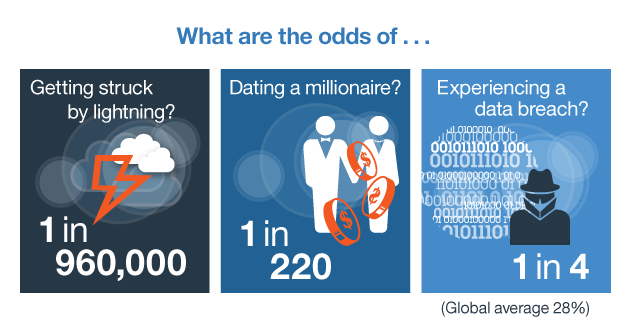
What are the odds of becoming the victim of a data breach?
What you can do to prevent data breaches
As a consumer, here are some tips to protect your personal information and decrease the chance of a data breach.
- Keep your software up to date.
Software companies issue updates when they fix security vulnerabilities. Download and install them to be protected from malware such as keystroke loggers. - Be careful about what links you click on in your email or when browsing the web.
You could inadvertently download malicious software to your phone or computer, or allow hackers access to your online accounts. Around 90% of malware comes from emails. StartMail deactivates links in emails to prevent accidentally clicking on scamming and phishing attempts. - Use Multi factor identification / 2 factor authentication.
This second step of authentication means you’ll have an added security layer to prevent others from logging into your accounts without your knowledge. - Encrypt sensitive data when storing it or transmitting it.
- Use unique and complex passwords
Use different username and passwords on each crucial site or service. Mixing upper and lower case, special characters, and numbers, or use multiple random word combinations. Use a password manager to help you remember the complex and possibly random passwords. - Try to limit the amount of data you share online as much as possible.
- Use Startpage.com to keep your internet searches private
- Use privacy respecting services and tools to protect your privacy. Educate yourself on what browsers, platforms, on online tools are best to use. We suggest that you check out a website like privacytools.io.
And last but not least:
- Use a secure email provider like StartMail to keep your private mail communication exactly that: yours and private!
StartMail offers the following privacy features:
- Ability to send private email to everyone. Even if your recipient does not use PGP encryption, you can still send encrypted messages with our Password Protected Message (PPM) feature.
- Unlimited disposable email addresses. When you don’t want to share your primary/real email address, you can create temporary ones on-the-fly. When email services send unwanted messages, simply delete the aliases and create new ones.
- State-of-the-art security. StartMail uses industry-standard security like TLS 1.2 and extra-secure vaults to keep your communications and data safe.
- Deleted is deleted. Once you delete your email it will be gone from our servers with 48 hours.
- Emails are stored in a super-secure vault.
- Based in The Netherlands. Subject to the strict Dutch privacy laws and the protection of European GDPR legislation.
Read more information on StartMail’s privacy page: “Privacy. It’s not just our policy. It’s our mission.“
Data breaches are here to stay – be prepared for them
Data breaches are the internet plague for users and businesses. They have been happening for years, and unfortunately, they will keep happening.
It is time for both companies and individuals to tighten security measures and better protect your personal data. You shouldn’t rely only on others to keep your information secure. Instead, invest in securing measures yourself. Become aware of the risks and take mitigating action.
StartMail offers email encryption for individuals and companies, protecting you from mass surveillance and unwanted intrusions. We believe that your privacy is a basic human right worth fighting for, and we made it our mission to do so!
More from the blog


Why Choose StartMail? – Privacy Matters! | Secure & Ad-Free
Continue reading
Protect Your Privacy as a Consumer – Top Tips
Continue reading
5 Best Privacy Gifts – Keep Your Data Safe & Secure
Continue reading